I’ve been meaning to write a review of Snagit for some time, but in advance of that, and having experienced some issues getting the Print Screen / PrintScreen / PrtScrn hotkey to work after setting up a new Windows 10 PC, I decided to blog what fixed the problem for me first.
In essence, the problem was that I could not allocate the Print Screen hot key to trigger Snagit Global capture, because every time I tried to set it, the program complained that the key was already in use by another Profile, or application. These different messages were confusing, especially as it was easy enough to confirm that ‘Print Screen’ was not a selected shortcut for any of my Snagit profiles! That left another application as the culprit.
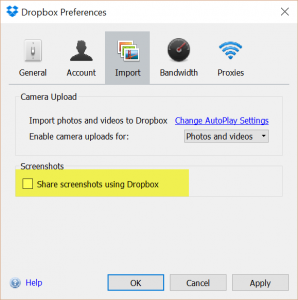
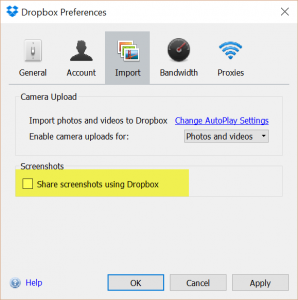
I was fearful that OneNote might be the cause, but I could not find any options mentioning Print Screen, and lots of web searches mentioned Dropbox… but I knew that I had already de-selected the option! (For reference, Dropbox may grab the PrintScreen and Ctrl + PrintScreen hotkeys to support its ‘Share screenshots using Dropbox’ function)
After much faffing, I found out that the problem seemed to be something to do with Dropbox retaining the hotkey allocation while it was running even if the option had been deselected!
The solution I found worked for me was to:
- Disable the ‘Share Screenshots’ option in the Dropbox Preferences window (Import tab);
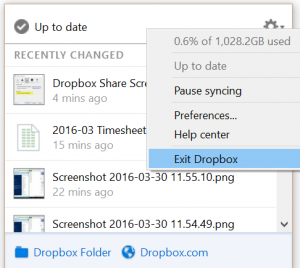
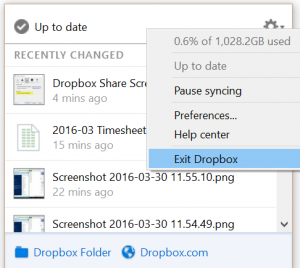
- Click OK on the dialog to make the changes and close the dialog, and then exit Dropbox (select ‘Exit Dropbox’ from the tools menu available from the Dropbox task bar icon;
- Now I opened the Snagit preferences, and after selecting Print Screen as the shortcut key for the Snagit Global Capture, I was finally able to save this setting!
- Then I restarted Dropbox by finding the app in the Start Menu and double-clicking to restart it.
I hope this helps someone!
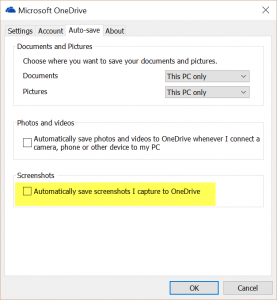
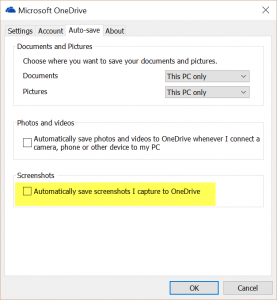
UPDATE 31/03/2016: Wouldn’t you know it, I had to reboot my PC overnight and after restart was once again greeted with a Snagit warning about a hotkey being in use by another profile! Turns out that Microsoft OneDrive had somehow nabbed it; I’m not sure how this is controlled… but when I pressed PrintScreen a OneDrive dialog appeared asking if I wanted to share my screenshots on my OneDrive. Answering ‘No Thanks’ seemed to free it up available for Snagit again. OK, I’ve found the Settings dialog, which like Dropbox is accessed from the Start Task Tray (normally at the right end of the Task Bar, near the clock):